Reality update: logik-imperialer-kriege-spr.png (2000×1391) … :
“ “
“
A praise of Folly – Security Theater and the OSI layers 8 and above
Early in February 2018 I was happy to give a speech at FOSDEM, in Brussels. They booked me after Howard Chu and right before the closing keynote – awesome, and there were a few thousand geeks in the audience – I guess that was the largest crowd I ever spoke to.
And I told them about “A praise of Folly: Security Theater – The mostly unknown OSI Layer 8 and above” – see References. Here’s my ongoing collection.
Reality update: logik-imperialer-kriege-spr.png (2000×1391) … :
“ “
“
You Can’t Handle the Truth About Facebook Ads, New Harvard Study Shows: https://theintercept.com/2018/05/09/facebook-ads-tracking-algorithm/
 … Do You Trust This Computer? … :
… Do You Trust This Computer? … :
“Science fiction has long anticipated the rise of machine intelligence. Today, a new generation of self-learning computers has begun to reshape every aspect of our lives. Incomprehensible amounts of data are being created, interpreted, and fed back to us in a tsunami of apps, personal assistants, smart devices, and targeted advertisements. Virtually every industry on earth is experiencing this transformation, from job automation, to medical diagnostics, even military operations. Do You Trust This Computer? explores the promises and perils of our new era. Will A.I. usher in an age of unprecedented potential, or prove to be our final invention?“
A New Kind of Memory Could Make RAM and ROM Obsolete … :
“The Chinese researchers say their new type of computer memory is not only the best of both worlds, but an improvement on the pair: It lets you decide how long you want the memory to hold data. “People in the future may receive a disc in which the data is only effective for, say, three days, which elevates the security of the information,” lead researcher Zhang Wei told China Daily. “People can also have tailor-made flash drives with the new storage technology. The data stored inside will be regularly emptied at an appointed time.”“
I am very sure you are great in breaking things? Iridium Browser, a project of +OSBA ev and many supporters, needs help in testing, QA – and even developers. I have been a user for many years, and I can recommend this Google-Free-Chrome.
Iridium Browser | A browser securing your privacy. That’s it. … :
“A BROWSER SECURING YOUR PRIVACY. THAT’S IT.”
“Iridium Browser is based on the Chromium code base. All modifications enhance the privacy of the user and make sure that the latest and best secure technologies are used. Automatic transmission of partial queries, keywords and metrics to central services is prevented and only occurs with the approval of the user. In addition, all our builds are reproducible and modifications are auditable, setting the project ahead of other secure browser providers.“
 Reality update: Casino Gets Hacked Through Its Internet-Connected Fish Tank Thermometer … :
Reality update: Casino Gets Hacked Through Its Internet-Connected Fish Tank Thermometer … :
“Nicole Eagan, the CEO of cybersecurity company Darktrace, told attendees at an event in London on Thursday how cybercriminals hacked an unnamed casino through its Internet-connected thermometer in an aquarium in the lobby of the casino. According to what Eagan claimed, the hackers exploited a vulnerability in the thermostat to get a foothold in the network. Once there, they managed to access the high-roller database of gamblers and “then pulled it back across the network, out the thermostat, and up to the cloud.”“
I know I have already posted this before, but this is important: Scott Galloway: How Amazon, Apple, Facebook and Google manipulate our emotions | TED Talk … :
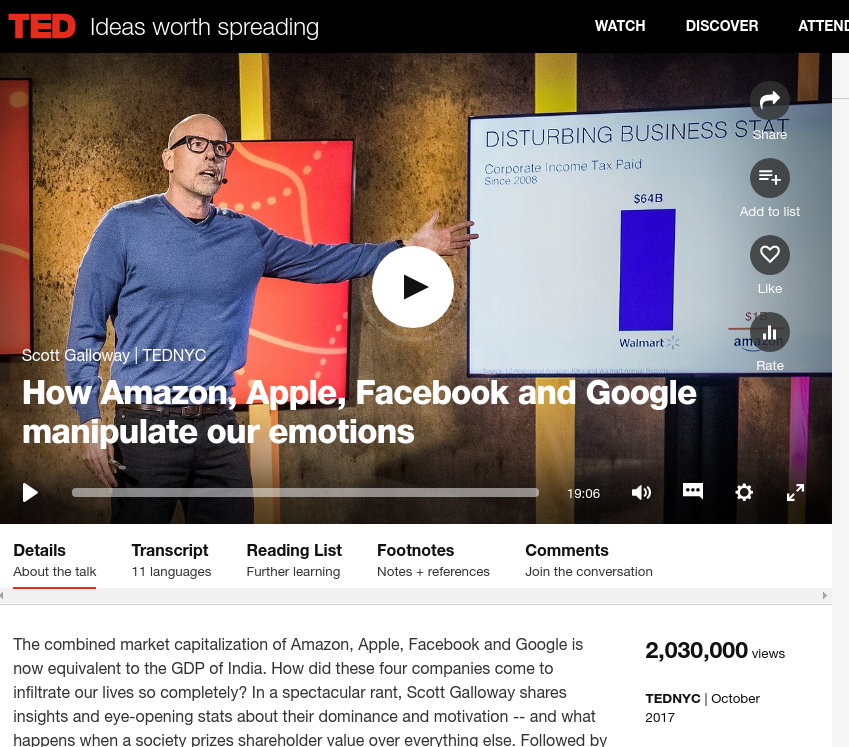 “The combined market capitalization of Amazon, Apple, Facebook and Google is now equivalent to the GDP of India. How did these four companies come to infiltrate our lives so completely? In a spectacular rant, Scott Galloway shares insights and eye-opening stats about their dominance and motivation — and what happens when a society prizes shareholder value over everything else.“
“The combined market capitalization of Amazon, Apple, Facebook and Google is now equivalent to the GDP of India. How did these four companies come to infiltrate our lives so completely? In a spectacular rant, Scott Galloway shares insights and eye-opening stats about their dominance and motivation — and what happens when a society prizes shareholder value over everything else.“
 You may have been thinking that the good old beep tool is safe, but you’re wrong …
You may have been thinking that the good old beep tool is safe, but you’re wrong …
Debian — Security Information — DSA-4163-1 beep:
“It was discovered that a race condition in beep (if configured as setuid via debconf) allows local privilege escalation.“
 … For years I have been talking about the dangers of QR codes…. well here’s one of the convenient Apple preload functions, I assume, messing it up: The Hacker News — Online Cyber Security News & Analysis … :
… For years I have been talking about the dangers of QR codes…. well here’s one of the convenient Apple preload functions, I assume, messing it up: The Hacker News — Online Cyber Security News & Analysis … :
“You need to open the Camera app on your iPhone or iPad and point the device at a QR code. If the code contains any URL, it will give you a notification with the link address, asking you to tap to visit it in Safari browser. However, be careful — you may not be visiting the URL displayed to you, security researcher Roman Mueller discovered. According to Mueller, the URL parser of built-in QR code reader for iOS camera app fails to detect the hostname in the URL, which allows attackers to manipulate the displayed URL in the notification, tricking users to visit malicious websites instead.“
 Reality update: Hackers Are Holding The City of Atlanta Hostage … :
Reality update: Hackers Are Holding The City of Atlanta Hostage … :
““This is much bigger than a ransomware attack, this really is an attack on our government,” Atlanta Mayor Keisha Lance Bottoms said at a news conference, Reuters reports. “We are dealing with a (cyber) hostage situation.”
(…)
Experts have warned that cybersecurity is likely the next great security threat for governments and companies around the world, and that most systems are simply not prepared. Indeed, Atlanta isn’t the first U.S city to be hit by ransomware — the Colorado Department of Transportation has already been hit twice in 2018. However, the Atlanta attack seems to the most thorough, city-wide cybersecurity breach yet. And though some companies have ramped up security following attacks, as Atlanta plans to do, it seems that most cities aren’t adapting their security before an attack happens.
(…)
It’s not yet clear at what point Atlanta will give in and pay the ransom to get its data back. But as more cities rely on digital processes, the dangers to both citizen privacy and security are going to multiply. Imagine a hack that takes out not just a city’s computer systems, but also its electrical power, plumbing, and even control of your own car.“
 Reality update: Microsoft to ban ‘offensive language’ from Skype, Xbox, Office | CSO Online … I doubt this is fine with German data protection laws:
Reality update: Microsoft to ban ‘offensive language’ from Skype, Xbox, Office | CSO Online … I doubt this is fine with German data protection laws:
“Better watch out if you are playing Xbox, get ticked, and cuss. Microsoft might ban you for the “offensive language.” If they do, then say bye-bye to your Xbox Gold Membership and any Microsoft account balances.“
 Gizmodo tells the story of a batch of sources being published that might have a sever impact not only on Brext… : AggregateIQ Created Cambridge Analytica’s Election Software, and Here’s the Proof … :
Gizmodo tells the story of a batch of sources being published that might have a sever impact not only on Brext… : AggregateIQ Created Cambridge Analytica’s Election Software, and Here’s the Proof … :
“Discovered by a security researcher last week, the files confirm that AggregateIQ, a British Columbia-based data firm, developed the technology Cambridge Analytica sold to clients for millions of dollars during the 2016 US presidential election. Hundreds if not thousands of pages of code, as well as detailed notes signed by AggregateIQ staff, wholly substantiate recent reports that Cambridge Analytica’s software platform was not of its own creation.“
 KIT (Karlsruhe Institute of Technology, Institut für Technikfolgenabschätzung und Systemanalyse) has published a great study that I haven’t read completely, but though it’s worth sharing: KIT – ITAS – Research – Project overview – Quattro S: Security, Safety, Sovereignty, Social Product … Especially regarding:
KIT (Karlsruhe Institute of Technology, Institut für Technikfolgenabschätzung und Systemanalyse) has published a great study that I haven’t read completely, but though it’s worth sharing: KIT – ITAS – Research – Project overview – Quattro S: Security, Safety, Sovereignty, Social Product … Especially regarding:
“This project will provide solutions for multiple problems. The first one is the security of information technology. The range of issues addressed includes zero-day exploits (e.g., WannaCry ransomware), denial of service attacks (e.g., Mirai), hardware attacks (e.g. based on the Meltdown and Spectre CPU flaws) up to novel types of hardware Trojans. The possibilities for these attacks originate from weaknesses in the long IT supply chains and threaten the confidentiality, integrity and availability of systems. The second problem is that these attacks can also threaten the safety of products, e.g., in energy infrastructures or in the automotive industry. The third problem consists of a loss of value added because of a migration of production and competences towards competing economies (e.g. US and China). Sovereignty would mean to have full control of the characteristics of information technology, to be sure that no hidden features are implemented, that no business secrets can be stolen, and to benefit economically from such control.“
 It’s been already six years that I wrote the Linux-Magazin article about hacking Android for banking data “Googles Smartphone-Linux ist ein einfaches Opfer für Angreifer“, and even a little more since me and Gunnar Porada met at Cortal Consors Bank. He was presenting, I was invited as a journalist.
It’s been already six years that I wrote the Linux-Magazin article about hacking Android for banking data “Googles Smartphone-Linux ist ein einfaches Opfer für Angreifer“, and even a little more since me and Gunnar Porada met at Cortal Consors Bank. He was presenting, I was invited as a journalist.
And the weird thing was: Cortal Consors, a big bank that in the past had specialized on trading stocks and stuff, had invited Gunnar to show us why SMS-TAN (Mobile TAN) and similar smartphone-based “Two-Factor-Auth” mechanisms are merely security theater, like every trick that includes the smartphone. Nevertheless, they said, they’d still recommend to use it, since “it is not actively being hacked”. Well, that has changed for sure in the last years. 🙁
Albeit this article is merely available in German, it’s a good read – have Google translate it. The following quote says basically that it’s less effort to hack both Windows PC and Android device (since they will be in the same Wifi sometime) than it takes to find out two devices belong together. I just realized that again, I had written about some topic that didn’t have a name then: CDT (Cross Device Tracking).
If you feel fine with Security by Obscurity, then SMS-TAN or Photo-TAN or Face recognition might be enough for you. It’s not for me.
“„Technisch ist das gar nicht so aufregend, die Angriffsmöglichkeiten sind bekannt. Das Schwierigste für den Angreifer ist eher herauszufinden, welches Handy zu einem infizierten PC gehört“, erklärt der Ex-Hacker, der gerade 100 000 Euro vom Konto eines Konzerns zu einer gemeinnützigen Organisation transferiert hat, mit gefälschten Accounts und Webseiten, auf die er den Demo-Rechner vorher per DNS-Spoofing umgeleitet hat – natürlich nur als Demo fürs Publikum.“
Zeynep Tufekci: We’re building a dystopia just to make people click on ads | TED Talk

“We’re building an artificial intelligence-powered dystopia, one click at a time, says techno-sociologist Zeynep Tufekci. In an eye-opening talk, she details how the same algorithms companies like Facebook, Google and Amazon use to get you to click on ads are also used to organize your access to political and social information. And the machines aren’t even the real threat. What we need to understand is how the powerful might use AI to control us — and what we can do in response.”
 Reality update: Cryptocurrency mining malware uses five-year old vulnerability to mine Monero on Linux servers | ZDNet … but hey, it is only PHP/Cacti:
Reality update: Cryptocurrency mining malware uses five-year old vulnerability to mine Monero on Linux servers | ZDNet … but hey, it is only PHP/Cacti:
“The cryptojacking campaign exploits CVE-2013-2618, an old vulnerability in Cacti’s Network Weathermap plug-in, an open source tool which is used by network administrators to visualise network activity.”
I’m still waiting for the first Linux Virus to hit the streets. Send it to me, please, if you have one. No, not the manual ones. They are boring.
Kaspersky’s ‘Slingshot’ report burned an ISIS-focused intelligence operation – CyberScoop
Hehehe: Kaspersky recently exposed US Intelligence Malware
“The U.S. government and Russian cybersecurity giant Kaspersky Lab are currently in the throes of a nasty legal fight that comes on top of a long-running feud over how the company has conducted itself with regard to U.S. intelligence-gathering operations.
A recent Kaspersky discovery may keep the feud alive for years to come.
CyberScoop has learned that Kaspersky research recently exposed an active, U.S.-led counterterrorism cyber-espionage operation. According to current and former U.S. intelligence officials, the operation was used to target ISIS and al-Qaeda members.”
undefined
(Thanks to Fefe)
 Iafrikan.com has a nice overview of the Facebook/Cambridge story so far. This story is full of links to the first-hand sources: How Facebook is killing democracy … :
Iafrikan.com has a nice overview of the Facebook/Cambridge story so far. This story is full of links to the first-hand sources: How Facebook is killing democracy … :
“A Cambridge Analytica executive explained: “There are two fundamental human drivers … hopes and fears … and many of those are unspoken and even unconscious. You didn’t know that was a fear until you saw something that evoked that reaction from you. Our job is … to understand those really deep-seated underlying fears, concerns. It’s no good fighting an election campaign on the facts because actually it’s all about emotion.”“
 Reality update: Sicherheitsproblem: Siri verrät Inhalte gesperrter Benachrichtigungen – Golem.de … :
Reality update: Sicherheitsproblem: Siri verrät Inhalte gesperrter Benachrichtigungen – Golem.de … :
“Solange Apple den Fehler nicht korrigiert hat, lässt sich das Problem nur beheben, indem Sperrbildschirmbenachrichtigungen für sensible Anwendungen deaktiviert werden.(…) Das Problem ist auch in der aktuellen Betaversion von iOS 11.3 vorhanden.”
(Only mitigation is to deactivate messages on the lock screen, also iOS 11.3 Beta is affected.)
If you understand Spanish, here’s the link to MacMagazine that discovered the flaw