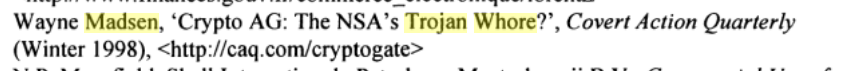
I dont understand all that fuzzin these days. This news is no news, almost everything about the Crypto AG stuff has been published in 1998 by Wayne Madsen, and has been uncloaked in the early nineties:
“The cover shielding the NSA-Crypto AG relationship was torn in March 1992, when the Iranian military counterintelligence service arrested Hans Buehler, Crypto AG’s marketing representative in Teheran. The Iranian government charged the tall, 50ish businessman with spying for the “intelligence services of the Federal Republic of Germany and the United States of America.” “I was questioned for five hours a day for nine months,” Buehler says. “
Here’s the link:
http://mediafilter.org/caq/cryptogate/
And here’s the source reference, if you need it.
as seen in the book “Shadow Government: How the Secret Global Elite Is Using Surveillance Against You” by Grant R. Jeffrey (avail on Google Books)
On Wayne Madsen – Wikipedia … :
“Wayne Madsen (born April 28, 1954) is an American journalist, author and columnist specializing in intelligence and international affairs.[1][2] He is the author of the blog Wayne Madsen Report.[3] He has been described as a conspiracy theorist.” (…)
“In 1990 Madsen joined Computer Sciences Corporation, working there from 1990 until 1997,[15] when he joined the Electronic Privacy Information Center (EPIC) as a senior fellow. In 1998, while at EPIC, Madsen was described by journalist Jason Vest in The Village Voice as one of the world’s leading SIGINT and computer security experts.[17] In late-January 2005, Madsen left EPIC.[15] While at EPIC he appeared as a guest on 60 Minutes,[18] ABC Nightline,[19] Voice of America,[20] and National Public Radio.[21]”