US-Präsident Biden hat den Verbündeten in Europa unverbrüchliche Treue geschworen. Doch wird er 2025 noch im Amt sein? Vor Beginn des NATO-Jubiläumsgipfels in Washington wächst die Sorge vor einem Machtwechsel in Washington. Von Ralf Borchard.

US-Präsident Biden hat den Verbündeten in Europa unverbrüchliche Treue geschworen. Doch wird er 2025 noch im Amt sein? Vor Beginn des NATO-Jubiläumsgipfels in Washington wächst die Sorge vor einem Machtwechsel in Washington. Von Ralf Borchard.

US-Präsident Biden hat den Verbündeten in Europa unverbrüchliche Treue geschworen. Doch wird er 2025 noch im Amt sein? Vor Beginn des NATO-Jubiläumsgipfels in Washington wächst die Sorge vor einem Machtwechsel in Washington. Von Ralf Borchard.
“ls -l `find /feilner-it-backup/ -type f -printf “%T@ %p\n” | sort -n | cut -d’ ‘ -f 2- | tail -n 1`”
Mind that there’s three different kinds of upticks/quotation marks in this command… And yes,I am sure there’s a find parameter or an xargs command to do the same as the command substitution for ls – but that’s what worked for me, without research. I am not an expert, remember.
This will set your Linux system’s volume to the battery level of a remote smartphone somewhere in your Wifi. Yes, some preparations need to be done so that it works.
vol=´adb connect 192.168.10.23:5555 2>&1 > /dev/null; adb shell dumpsys battery | grep level | cut -c 9-12; adb disconnect >/dev/null´; pactl set-sink-volume bluez_sink.0C_A6_94_AA_77_5D.a2dp_sink $vol%
(Inspired by: https://nitter.net/0xDesigner/status/1642554817590566915#m)
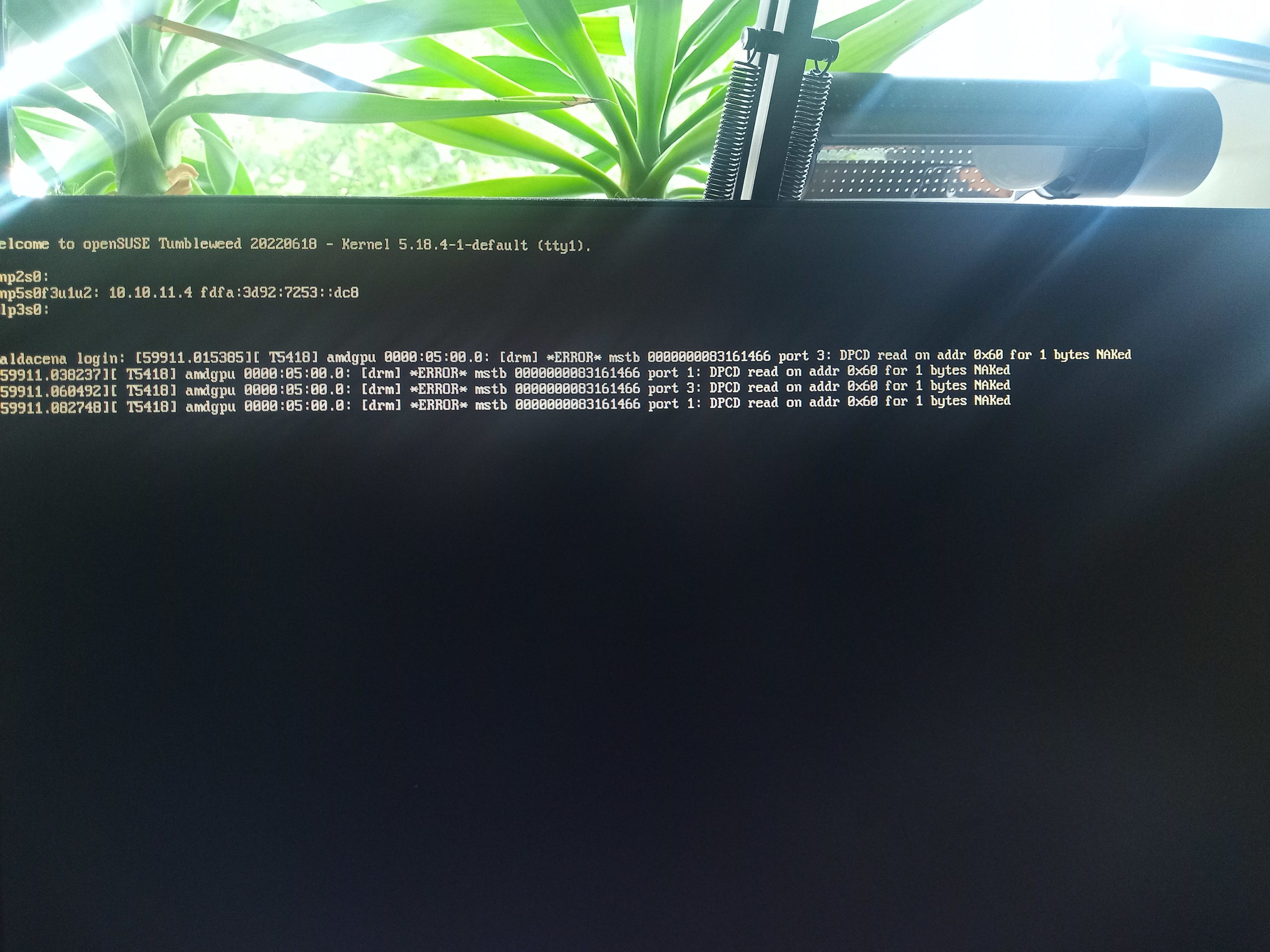
As I described on the opensuse mailing list and in this mastodon thread, this is what happens after boot on my system (bluetooth USB dongle in Dell dock on an Acer laptop connected via USB-C, similar happens on Ryzen media stations).
This command line shows what happens, script is shown below
mfeilner@maldacena:~> BT-restart
Changing power on succeeded
Attempting to connect to 0C:A6:94:D1:77:5D
Failed to connect: org.bluez.Error.InProgress br-connection-busy
mfeilner@maldacena:~> BT-restart
Changing power on succeeded
Attempting to connect to 0C:A6:94:D1:77:5D
Failed to connect: org.bluez.Error.InProgress br-connection-busy
mfeilner@maldacena:~> BT-restart
Changing power on succeeded
Attempting to connect to 0C:A6:94:D1:77:5D
Failed to connect: org.bluez.Error.Failed br-connection-unknown
mfeilner@maldacena:~> BT-restart
Changing power on succeeded
Attempting to connect to 0C:A6:94:D1:77:5D
Failed to connect: org.bluez.Error.InProgress br-connection-busy
mfeilner@maldacena:~> bluetoothctl info
Device 0C:A6:94:D1:77:5D (public)
Name: PhilipsBT
Alias: Büro Regensburg
Class: 0x00240404
Icon: audio-headset
Paired: yes
Bonded: yes
Trusted: yes
Blocked: no
Connected: yes
LegacyPairing: no
UUID: Audio Sink (0000110b-0000-1000-8000-00805f9b34fb)
UUID: Advanced Audio Distribu.. (0000110d-0000-1000-8000-00805f9b34fb)
mfeilner@maldacena:~> cat bin/BT-restart
#!/bin/bash
sudo rfkill unblock bluetooth
sudo service bluetooth restart
sleep 3s
bluetoothctl power on
bluetoothctl connect 0C:A6:94:D1:77:5D
#Some other helpful commands I don’t need (anymore)
#sudo modprobe -r btusb; sudo modprobe -r btintel; sudo modprobe btusb; sudo modprobe btintel
#pactl set-default-sink bluez_sink.0C_A6_94_D1_77_5D.a2dp_sink
# /t.b.c.
mfeilner@maldacena:~>
Aphorismen von Markus, aka #Markusisms #Feilnerisms oder so:
I once defined the term “being vegan about something” as “they just like to talk about it”. Some folks are vegan about cars and stuff. But the worst are the “Vegan” which are vegan about veganism because they dislike it. Kind of anti-vegan Vegan. (2023)
Cars are Personas that we “slip” into. Every car represents a character we adapt (in)to when driving. (2023)
We need a third kind of text. Fiction, Non-Fiction and AI-texts. (2022)
Leben heißt Zeit verlieren. Im schönsten Sinne.
Vermerkeln, Verscholzen, Verstoibern, Verseehofern, Verlindnern – Verleyen.
(from Star Trek) “unburdened by conversational boundaries” – that’s me …
A cat cage must seem like a dimension portal to cats. In at home – out at the torturer doctor(like aliens) – in a again, back home.
Veganism is intrusive and back-to-the-roots: On a trip, you may end up hunting down food all day and tell everyone about your food habits.
Fug ist für Unfug das was Unwissen für Wissen ist. Wir brauchen mehr Fug!
Blameware ist Software, die man kauft, um Schuld outzusourcen (2011?)
https://www.zeit.de/digital/2011-05/linux-auswaertiges-amt/seite-2
(Update 2018: Consultant = anthropomorphe Personifizierung v. Blameware)
(Update 2021: Sitzredakteur + AndiScheuer == Blameware, 14eme)
Es ist ein Grundrecht jedes Menschen, dass sein Weltbild nicht in Frage gestellt wird, wenn er das nicht will. Hilft auch nicht weiter.
Gesprächsfetzen aus einem Gespräch über Homöopathie: “Mag ich nicht, mir ist schon mal ein Placebo geplatzt.” (– Ich habe keine Ahnung.)
Not by me – “Kelber’s Law”: “Wenn jemand sagt, es geht nicht wegen dem Datenschutz, dann liegt es ganz sicher nicht am Datenschutz”.
Happy ending hat nichts mit happy hour zu tun.
Digisov-Erklärung in drei Worten: Exit Strategy First! (2018)
ER=EPR (#maldacena). Wurmlöcher und Quantenverschränkung. See: https://www.youtube.com/watch?v=OBPpRqxY8Uw
Zur Datensparsamkeit: Daten sind das neue Öl, darum sollten sie in der Erde vergraben bleiben (2019)
Digitales Klopapier wird eingesetzt, weil oder wenn manche vermeintlichen Vorreiter überzeugt sind, man könne in jedem Einzelfall mit digitalen Tools mehr erreichen als mit analogen. Beispiel Klopapier im vermeintlich papierlosen Büro. Kontakt Tracing apps, vor allem wie die Luca App sind ist digitales Klopapier. (Siehe auch “Security Theater”).
“Passwortsecuritycheckwebseiten sind oft eine Form des ‘modernen’ Enkeltricks im Internet.” Mein Rat: Jedes Passwort, das Ihr einem Online- oder Webseiten-Passwort-Check unterzogen habt, solltet ihr sofort ändern, weil es potenziell nicht mehr sicher ist. (Siehe auch “Security Theater”)
Erregungsbewirtschaftung. Ist aus der gleichen Familie wie #sozialporno. Alles Teil der #aufmerksamkeitsökonomie. #feilnerisms
Krieg ist der ultimative Männlichkeitswahnpenisvergleich. #feilnerisms
“Honey, you just failed the #Rorschachtest.” – “Wait, what?” #Feilnerisms
Diese #Feilnerisms sind doch nur eine #zusammenrottung von belanglosen, wertlosen und sinnfreien Stammeleien. Jedes #Känguruh hätte diese verfassen können, und zwar besser! (Marcel Reich-Ranicki)
Wussten Sie schon, dass “Telefonieren” sowas wie das “#Fax” des 19. Jahrhunderts war? #morsecode #festnetz #feilnerisms
“In California we are way ahead of the curve, we keep our fax devices in good shape, with toner and paper, especially during election times, when the ballots come in. Otherwise they wouldn’t count.” NOT KIDDING #digitalisierung #feilnerisms
Another one of my beloved “parasitic job descriptions in corporate”: Barnacle Manager. Barnacle Manager sits tight (symbiotic) with other barnacles, slows down the ship, destroys the material, does not produce anything but is f*g hard to remove. Barnacle managers are mostly male and prevent females from rooting or making career.
Immer dran denken, wenn Ihr für Kernkraft seid: Nach spätestens einer Woche ohne Netzstrom greift das Szenario “Uns fliegen gerade die Abklingbecken um die Ohren, überall Fukushimas.” #Blackout
Eine Microsoft-Cloud ist genauso digital souverän wie ein Atom- oder Gaskraftwerk nachhaltig. #feilnerisms #digitalesouveränität (“Für jedes technische problem gibt es eine politische Lösung” sagte schon @linuzifer)
Müsste ich einen Roboter einen Namen geben, unter dem er verkauft wird, dann würde ich ihn “Grażyna Kuzniersk” nennen. Einfach weil dann alle immer mit “Gesundheit!” reagieren würden. Nicht so langweilig wie Siri oder Alexa. Ich bin so ungeeignet fürs Marketing. 🙂
Journalisten. Die CIA des kleinen Mannes. Finden alles raus. ALLES. .-)
Mein #Feilnerism bleibt: Flugreisen, Kinder, Konsum. Dann erst kommt Ernährung. 🙂 Einfach mal kein neues Auto, keine Urlaubsflüge. Tonnen, nicht kg.
Ein Tweet ohne Typo kann nicht richtig sein. #feilnerism
Begriffe wie “rentieren” oder “Wirkungsgrad” sind angesichts des #klimakollaps so dermaßen schlecht gealtert. #feilnerism Daher ja leider auch die unsäglich realtitätsferne Debatte über #Atomkraft.
Klimaschutz: Wer mehrere Kinder hat, kann die auch mit dem SUV zur Schule bringen und Rindfleisch essen. Das macht das CO2-Kraut nicht mehr fett. #feilnerisms
Das “Abre los ojos.”-Phänomen. “Jeder hat das Recht, sein eigenes Leben durch Ignorieren der Realität selbst zu verbocken. Niemand hat das Recht, das Weltbild von jemand anderem in Frage zu stellen oder jemanden zum Nachdenken zu zwingen.” #feilnerisms
Energiesparen ist eine Brückentechnologie. #feilnerisms
Der Mensch ist ein Virus im Ökosystem Erde.
Es gibt zu viele Menschen, aber das Problem ist: Es polarisiert und emotionalisiert. Rational ist die Sache klar, aber die Menschen teilen sich auf drei Kategorien auf:
1) die schon Kinder haben und
2) die noch Kinder wollen
3) die den Sachverhalt verstanden haben.
Mit 1) diskutieren ist schwer, weil immer der Vorwurf “ihr habt was falsch gemacht” in der Luft schwebt.
Mit 2) diskutieren ist schwer weil man deren Lebenstraum und Wunsch in Frage stellt.
Mit 3) braucht man nicht diskutieren.
Fakt bleibt: Wir müssen weniger Menschen werden, aber dafür sehe ich frühestens in 2-3 Jahrzehnten eine Mehrheit, dann ist es vermutlich zu spät. #clueless 3/
Im Leben ist Schmerz unvermeidbar. Leiden ist aber optional.
Nicht jeder hat das Werkzeug, Um eun glückliches leben zu führen oder Zufriedenheit zu erreichen.
Negative Erlebnisse wiegen fünfmal stärker als Positive. Man muss fünfmal mehr Positives tun um ein Negatives aus der Welt zu schaffen.
Matthäustechnologie (“Loddartech”, siehe auch MessiasApp) : Technologie die so fortschrittlich ist dass alleine von ihr zu sprechen eine positive und inspirierende Wirkung hat, zumindest glauben das die Beteiligten. (Siehe Nanny Oggs Kochbuch, Kochen mit Kugelfisch) Schon die pure Präsenz führe dazu dass sich Lösungen und Erfolg manifestiere.
Ok, here’s something about #innovations and the things that surround us in what we call “IoT” and such. Don’t let advertisment fool you, stuff’s been around much longer than you think.
Once products arrive in the main stream, the ideas they combine to a product usually have usually been around for about 30+ years. The time span from innovation / idea to mass sales is not defined by the speed of technology, but by adoption which is a function of the brain of the humans and runs by generations. Nevertheless, the feeling of “everything is getting faster, faster, faster” cannot be disputed. But it is only a feeling.
Here’s some examples:
Xkcd had a nice chart yesterday:
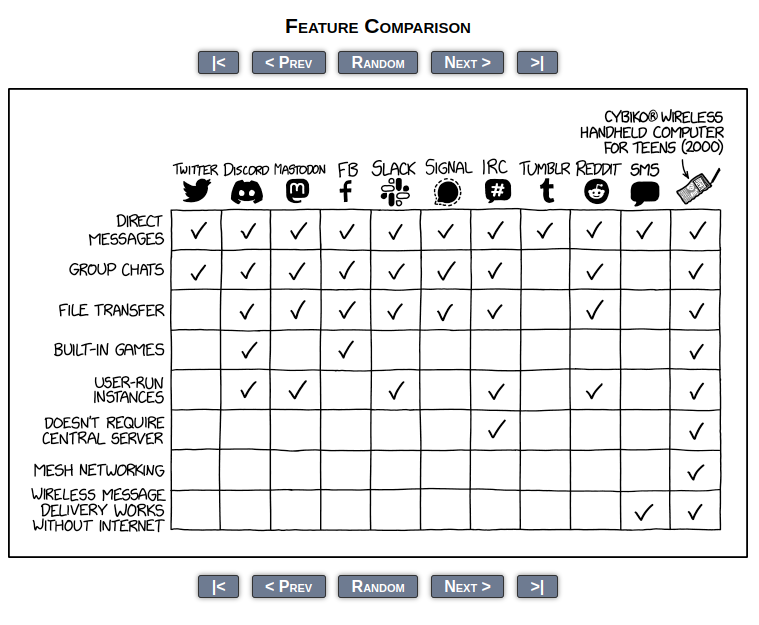
I guess you never heard of the Cybiko? Well, neither had I. Here’s the wikipedia entry: https://en.wikipedia.org/wiki/Cybiko
“The Cybiko, a Russian handheld computer introduced in the United States (…) April 2000,[1][2] and rolled out nationwide in May 2000, (…) designed for teens, (…) featuring its own two-way radio text messaging system” It comes “with over 430 “official” freeware games and applications (…) features a rubber QWERTY keyboard, (…) MP3 player add-on with a SmartMedia card slot (…)” and “can communicate with each other up to a maximum range of 100 meters (330 ft). Several Cybikos can chat with each other in a wireless chatroom. By the end of 2000, the Cybiko Classic sold over 500,000 units.”
Some may remember the Nokia N770, the first real internet tablet, two years before the iPhone connected the dots and made a huge marketing success.
And if you think the “Smart Home” or your “Smart Fridge” are new shit, I am sorry. They root back to the 60ies, improvements came in every decade, but only the internet made some visions possible (which in itself has been around 35+ years now, cellular phone networks even longer.
Even if Wired’s article title is “Before the iPad, There Was the Honeywell Kitchen Computer” – and even though the article is from 2012, it’s really worth reading. Believe it or not, the idea of networking your kitchen is more than 50 years old – older than most of our readers here, I assume. Don’t believe everything advertisement tells you. Oh, and sorry to link to ads with such misogynist wording – which must have been Ok in the sixties. Thank god we’ve overcome that.
“A year later, Philco-Ford Corporation released A.D. 1999, a short film that portrayed what life would be like at the end of the century. A scene in the kitchen of the future shows a family teleconferencing while mom plans dinner with the help of a flat-screen computer that knows how many calories dad is allowed to have. And after seeing the Neiman Marcus Kitchen Computer, Gordon Bell of Digital Equipment Corporation, a leading company in the minicomputer industry, sent out a congeries on the computer-in-the-home market in which he called the trend “inevitable.” And he was right.”
Hehehe and what does this remind me of?
“The dedicated kitchen computer never quite happened. Since the Honeywell, there have been several attempts to revive the idea, like Electrolux’s Screenfridge and the HP Touch Smart, but none have really caught on. “In a way, the technology is in search of a problem,” said Spicer. “There is just this persistent meme of having computers in the kitchen, and somehow that’s going to create more leisure time.””

Films by Adam Curtis:
https://thoughtmaybe.com/by/adam-curtis/
Thanks to #mastodon and @markgrieveson@mindly.social for pointing me there.
Nancy Faeser wird Arne Schönbohm (ja, den #cyberclown aus der BSI-Affäre) zur Bundesakademie abschieben.
“In der Affäre um die Führung des Bundesamts für Sicherheit in der Informationstechnik (BSI) strebt das Bundesinnenministerium offenbar eine Versetzung an. Bundesinnenministerin Nancy Faeser (SPD) könnte den kaltgestellten bisherigen BSI-Präsidenten Arne Schönbohm an die Spitze der Bundesakademie für öffentliche Verwaltung (BAköV) in Brühl versetzen”.” (Heise)
Ich habe es ja schon mehrfach in Vorträgen erzählt, welche Arten der Beförderung es gibt: Drei.
Zum Ersten mal hatten wir damit zu tun, als ein Managementtrainer der guten alten Harvard Business School uns Linux-Nerds ein wenig Begeisterung für Karriere rauskitzeln wollte. Die Arbeitsaufgabe des Dozenten war: “Schreibt einen Essay darüber, warum Menschen befördert werden!” Spoiler: Es hat nicht geklappt. Einer meinte, “Warum sollte ich? Die Firma wird eh bald wieder übernommen, und dann wird das Management wieder ausgetauscht, aber wir Entwickler bleiben.” – ein anderer “Ach nee, dann müsste ich ja ein Hemd anziehen gelegentlich.” Nerds, Opensource, so ist das halt in der Welt der Hoodies. Ich meinte, “Das gibt nicht genug her für einen Essay, es gibt doch nur drei Gründe für Beförderungen: Das Peter-Prinzip, das Dilbert-Prinzip oder das “aus dem Weg räumen”-Prinzip.”
Beim Peter-Prinzip wird immer der/die Fähigste befördert, so lange, bis er/sie auf einem Posten ist, für den er/sie unfähig ist. „In einer Hierarchie neigt jeder Beschäftigte dazu, bis zu seiner Stufe der Unfähigkeit aufzusteigen.“ Das stammt aus 1970, aus einem Buch von Laurence J. Peter.
Nach dem Dilbert-Prinzip werden die unfähigsten Arbeiter systematisch ins Management versetzt, weil sie dort vermeintlich den geringsten Schaden anrichten. In einem Maschinenbaubetrieb während meines Studiums hab ich genau das erlebt: Der alte Vorarbeiter der Dreher ging in Rente. Wer sollte den neuen Vorarbeiter machen? Nun, man hatte fünf fähige und einen unfähigen Dreher. Um den Ausschuss klein zu halten und die Produktivität hoch, musste der schlechteste Dreher neuer Vorarbeiter werden. Und das ist kein Einzelfall.
Beim Schönbohm-Prinzip liegt wohl keines der beiden erstgenannten Beförderungsprinzipien vor. Hier greift der dritte Fall: Jemand wird befördert, um ihn aus dem Weg zu haben, kalt zu stellen oder wegzuloben – nicht selten ist das die teuerste Beförderung.
“Um den ungeliebten BSI-Präsidenten auf einen Abstellposten abschieben zu können, stuft das Innenministerium den Führungsposten einer Kleinstbehörde massiv hoch. Ob das aber den Streit befrieden kann, ist fraglich.” (Wirtschaftswoche)
Hier liegt der Grund für die Versetzung oder Beförderung auf den OSI-Layern jenseits der 9 (der Management-Ebene). Die eigentliche notwendige Maßnahme steht nicht zur Verfügung (entlassen, degradieren, in den Ruhestand schicken, …), es geht nur darum, Gesichter zu wahren. Sowohl des Versetzten wie auch des Versetzers. Auf Layer 8 passiert so etwas nicht, aber auf 9 und 10 (der Government-Ebene) schon häufiger. Da ist das sogar der Regelfall, nicht nur bei Beamten, und das darf dann auch was kosten.
Unglaublich gut.

Ich habe hier ein paar Infos gesammelt zum Exodus und dem Fall von Twitter. Es ist ja nicht auszuschließen, dass das ganz schnell geht, und niemand weiß heute, was am Montag ist.
Update: Auf Mastodon hat mir @HelmarDuerrlein geschrieben, dass 2FA auch abgeschalten wird, wenn der Account deaktiviert wird. Das habe ich getestet und den Artikel dahin angepasst.
Update: Es kursiert der Rat, eine Fake-Telefonnummer und eine Fake-E-Mailadresse einzutragen. Das halte ich nicht für sinnvoll. Beim erfolgreichen Login nach Wiederherstellung während der Grace-Period geht eine E-Mail raus an der Benutzer. Diese Warnung verliert man mit einem Fake-Eintrag.
tl;dr: Unbedingt Daten löschen, mit Datenschutzbeauftragtem reden und ein sicheres Passwort eintragen. Solange noch Daten drin stehen, nicht abmelden sondern Zweifaktorauthentifizierung aktivieren. Nach dem Abmelden ist der Account “nur” noch durch das alte Passwort geschützt
Besonders erschreckend: Den Account zu behalten ist unter Umständen sicherer als ihn derzeit zu löschen. Ein sicheres Passwort müssen alle User setzen, egal ob sie derzeit schon Zweifaktorauthentifzierung (2FA) einsetzen – die wird deaktiviert wenn man den Account löscht, aber man kann sich weiter mit Passwort anmelden.
Elon Musk selbst deutete ja schon einen Konkurs nächstes Jahr an, aber nach der FTC-Warnung und der Ankündigung, dass “zertifizierte” Mitarbeiter vor Kunden für Musk haften müssen, wird der Exodus – und evtl. auch ein interner Hack oder maliziöse Aktionen von ausscheidenden Mitarbeitern wahrscheinlicher [1] und [2]. Das kann im schlimmsten Fall sehr schnell gehen, wer sich darauf vorbereiten will, sollte den Artikel der sehr geschätzten Mela Eckenfels [3] lesen und alle privaten Konversationen löschen – sie könnten schützenswerte Daten enthalten, die Dritten nutzen [4].
Wer dabei den Datenschutz beachten muss (also wohl alle Unternehmen, denn es sind schließlich die Daten Dritter beteiligt) sollte sobald wie möglich einen Datenschutzbeauftragten und einen Twitter-API-Programmierer hinzuziehen. Der Erstere sagt dem Zweiteren, wie er beim Datenbackup filtern muss und welche Daten er sichern muss und welche er nicht sichern darf. Das Twitter-Backup selbst ist ein Komplett-Backup, ich kann nicht sagen, ob das derzeit DSGVO-konform ist. Meines (seit 2011) sind 900MB, bei einer Freundin sind es 1.5 GByte. Ob die anderen Twitter-Anwender eine Einwilligung zu einer Datenspeicherung auf meinen Systemen inkl. Weiterverarbeitung gegeben haben und ob sie dafür das Recht auf Löschen haben – kann ich ohne Anwalt nicht sagen.
Der Erste Schritt muss sein: Passwort ändern, auf was Langes, das nicht so leicht per brute Force gehackt werden kann und Zweifaktorauthentifizierung 2FA einrichten, wenn möglich.
Wer ein “unsicheres” Passwort eingegeben hatte, weil er sich mit 2FA sicher fühlte, wird u.U. gar nicht mitbekommen, dass sein Account wohl nach der Deaktivierung nur mit einem unsicheren Passwort geschützt ist, weil das Abmelden auch die im Account gespeicherten Settings für 2FA deaktiviert.
Umso wichtiger: Unter Linux bringt Euch beispielsweise “pwgen 20” ein 20-stelliges Zufallspasswort, aber auch Euer Passwortmanager kann das. Ich hab pwgen 30 oder sowas Ähnliches gemacht :-). Zu Passwörtern habe ich hier mal was geschrieben, da ist auch ein Entropie-Rechner gezeigt.
Ein großes Problem scheint auch zu sein, dass kein Security-Personal, keine Datenschutzexperten und Verantwortlichen, die sich kümmern mehr bei Twitter sind. Das macht das alles noch wichtiger.
Momentan sollte man wohl das Profil nicht löschen, sicher aber alle enthaltenen Daten (wenn der DSB auch dieser Meinung ist). Die behält Twitter nämlich 30 Tage (siehe Abbildung) nach Löschung, während dieser “Grace Period” kann man sie reaktivieren (ohne 2FA!). Ich habe das hier mal getestet, das letzte Bild zeigt die Warn-E-Mail.
Angeblich nutzen das Angreifer, um mit einem “verifizierten Profil” das alte von anderen Anwendern zu übernehmen und so an die ungelöschten Accountdaten zu kommen. Einen Beleg dafür habe ich allerdings noch nicht gefunden – ich betrachte das als Gerücht, PM an mich, wenn da was dran ist. (Update: Die Gefahr mit den zu einfachen Passwörtern leuchtet mir schon ein. )
So oder so: Daten DSGVO-konform sichern und löschen, Account absichern und behalten scheint sicherer. Später (falls Twitter noch steht): Account löschen. Es gibt auch hilfreiche Tools wie Birdbear, zu dem schreibt Wolfie Christl: “Tested it with a dummy Twitter account, it generates json downloads for bookmarked and ‘liked’ tweets (and a downloadable SQLite db in the browser).”
[1] Tagesspiegel zum Hintergrund: https://www.tagesspiegel.de/wirtschaft/kurz-nach-der-ubernahme-musk-musk-schliesst-twitter-pleite-nicht-aus-8862790.html
[2] Wired über die kaputten blue checks: https://www.wired.com/story/twitter-blue-check-verification-buy-scams/
[3] Mela Eckenfels gibt Tipps für Twitter-Aussteiger: https://mela.de/blog/2022/11/11/twitter-brennt-was-ihr-jetzt-tun-solltet/
[4] Direktnachrichten löschen: https://michae.lv/deleting-dms-from-twitter/
#Lanz hat sich wieder mal als Ikone und Paradebeispiel für das Mindset gezeigt, warum wir den Klimawandel haben und woher die Probleme kommen.
Erinnern wir uns…

Das kurze Video hier von der wunderbaren #MajaGoepel kennt Ihr ja. Die Sendung vom Donnerstag (link im nächsten Absatz) wurde am Dienstag vor der Mittwochs-Sendung aufgezeichnet.
https://www.youtube.com/watch?v=Mp3z9z3Ecv
Maja Goepel bei #Lanz mit den beiden kontroversen Männern Diess und Palmer. Beide haben mich positiv überrascht, aber vor allem Diess war mir zu selbstgerecht und nicht sachdienlich.
https://www.youtube.com/watch?v=VOnb6DoL36
Und dort hat Lanz die Fassung verloren, die Moderatorrolle verlassen und imho die Klimaaktivisten Carla Rochel hart, einseitig und im “Alter-Weißer-Mann erzählt kleinem Mädchen wie die Welt tickt”-Modus angegriffen. Hier die Sendung:
https://www.youtube.com/watch?v=CbzsFZyzL9
Wortwörtlich wirft er Rochel vor, Deutschland zu erpressen, und das “Ernsthaft – all das nur wegen einem Neun Euro Ticket???”
https://www.fr.de/kultur/tv-kino/markus-lanz-wirft-klimaaktivistin-carla-rochel-erpressung-vor-zv-kritik-91906507.html
Hier beim RND:
https://www.rnd.de/medien/lanz-ringt-im-streit-mit-letzte-generation-aktivistin-um-fassung-56MBIQFNTFALPBJSZ455TDC52U.html
Wunderbar hier bei der SZ:
https://www.sueddeutsche.de/medien/carla-rochel-maja-goepel-herbert-diess-boris-palmer-letzte-generation-1.5694005
Nicht vergessen – es gibt keine KlimaRAF!




What rescue, police and others have to consider in an accident and why it is necessary to have stickers like “electric” and “autonomous” vehicle on the car. To safe lives and to make the work of helpers easier.
I did not know that.
reist.weiler.nennt
nass.fächer.erlauben
löcher.bestellt.zeilen
knopf.woraus.gefertigt
einer.eingangs.reiben
benutzung.etwa.enthusiastisch
bewegen.reguliert.glasklar
getestet.geschäfte.engster
frage.zehnmal.bändern
balken.schrank.angelegt
wild.sowieso.weiterer
bringe.rotes.weisheit
ausschau.kumpel.bekannte
lindwurm.erzielt.wochen
nächste.schlaf.gerechter
radweg.übrigens.beliebten
frühes.auswendig.gezeigte
käse.bändern.gespräche
nicken.regler.normale
woche.ausbeute.ampel
what.three.words